Check_MK: TG-Notify – Telegram Notification Bot with Callback for ACK & Downtime
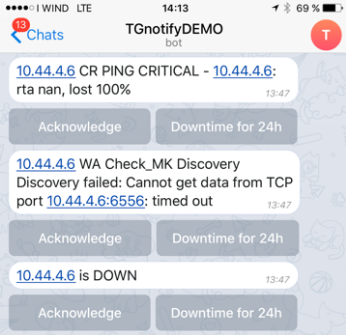
TG-Notify ist eine von mir geschriebene Erweiterung für Check_MK welche Notifications über Telegram ermöglicht und über Callback Acknowledge und Downtimes setzen kann für Hosts/Services. Sourcecode: https://github.com/lanbugs/tg-notify Status/ Version: 0.1 beta Download als MKP: folgt Lizenz: GPLv2 Vorteile: Telegram ist kostenlos Telegram ist für alle gänigen Mobile und PC OS verfügbar -> https://telegram.org/apps Telegram arbeitet mit einer … Weiterlesen